IT compliance: understanding the scope and challenges
What is IT compliance and why has it become critical?
IT compliance refers to all the measures, processes and controls put in place to ensure that your information system complies with laws, regulations, standards and contractual commitments which are applicable to it. It is a transversal discipline that involves technical architecture, data governance and organizational processes.
It is structured in three dimensions:
- The dimension regulatory includes legal obligations: RGPD, NIS2, sectoral laws.
- The dimension normative covers voluntary standards that often become essential: ISO 27001, SOC 2, PCI-DSS.
- The dimension Contractual integrates the security clauses imposed by your customers or partners during tenders.
Why did the stakes get so much tougher? For 3 reasons:
- the Toughening of sanctions (European regulators have issued several billion euros in GDPR fines since 2018);
- The Complexification of IS with the cloud and SaaS that multiply the number of control points;
- The Mediatization of incidents that makes non-compliance visible beyond the regulatory circle.
As accounting must meet standards and be audited, IT must now prove compliance in a rigorous and documented manner.
The risks of non-compliance: beyond fines
For the most serious infringements, the RGPD provides for fines of up to 20 million euros or 4% of global annual turnover, whichever is greater. In 2021, Amazon was the subject of an initial fine of 746 million euros pronounced by the Luxembourg authority, a decision contested by the company. Meta, Google, and other big companies have also been heavily sanctioned. Now, regulators no longer hesitate to strike hard.
But the risks go far beyond the financial side, because a compliance gap can block a tender if your customer requires a ISO 27001 certification that you don't have. He can trigger legal actions from injured persons through a personal data breach. It may lead to an injunction to stop certain treatments, with immediate operational consequences. And it generates a reputational risk whose media coverage can far exceed the amount of the fine itself.
The calculation is actually quite simple: it is cheaper to adopt a proactive compliance approach than to have to carry out emergency remediation, not even counting the associated sanctions and business losses.
Compliance and performance: how to reconcile them?
The most mature organizations have understood that well-managed compliance clarifies responsibilities, reduces the risk of incidents that completely paralyze business, and creates a framework of trust that facilitates partnerships. Integrated from the design of projects (Compliance by design), it avoids late resumes and costly blockages.
On the commercial side, the ability to prove compliance during tenders has become a differentiating argument in the face of less mature competitors. Compliance and performance are not opposed; they are reinforced when compliance is automated as much as possible and integrated into IS governance.
Mapping the main IT compliance requirements
RGPD: personal data protection and responsibility
The General Data Protection Regulation (GDPR) imposes specific technical and organizational obligations. For IT, this means:
- traceability of personal data in all systems;
- ability to respond to requests for rights (access, deletion, portability) within one month, extendable by two additional months in the event of a complex request;
- maintenance of an exhaustive treatment register.
Any data breach must be notified to the appropriate authority within 72 hours of the discovery of the incident. In addition, data protection impact assessments (AIPD or PIA) are mandatory for high-risk treatments. Finally, contracts with cloud providers such as Microsoft must include specific subcontracting clauses.
NIS2 and cybersecurity: the new obligations for critical sectors
The NIS2 (Network and Information Security 2) directive significantly expands the scope of NIS1. It now covers essential sectors (energy, transport, health, health, health, finance, digital infrastructures) and important sectors such as the post office, waste management or industrial manufacturing.
Logically, the obligations that follow are substantial: formalized cyber risk management, securing supply chains, early warning within 24 hours followed by detailed notification within 72 hours, and cyber governance brought to management level (not just IT teams).
ISO 27001, ISO 27701 and other standards: voluntary compliance as a competitive advantage
ISO 27001 defines the international framework for the Information Security Management System (ISMS). It structures 93 controls divided into four themes (organizational, technological, human and physical) according to the version ISO 27001:2022. Its certification by an accredited body is increasingly required in public and private tenders.
Its extension, the ISO 27701, specifically addresses the protection of personal data and is a structuring complement to the RGPD. SOC 2, an American standard often required by international customers, covers security, availability and confidentiality. As for PCI-DSS, it is mandatory for all card payment processing. Finally, HDS (Health Data Hosting) is the essential French certification for hosting medical data.
Although these standards are theoretically voluntary, in practice, they are prerequisites for accessing certain markets.
Methodology: structuring your IT compliance process
Step 1 — Map applicable requirements and prioritize
You can only comply with what you have clearly identified. The first step is to draw up a precise inventory of the requirements that apply to your organization :
- sector of activity;
- geography;
- nature of the data processed;
- certifications required by your customers;
- security contract clauses.
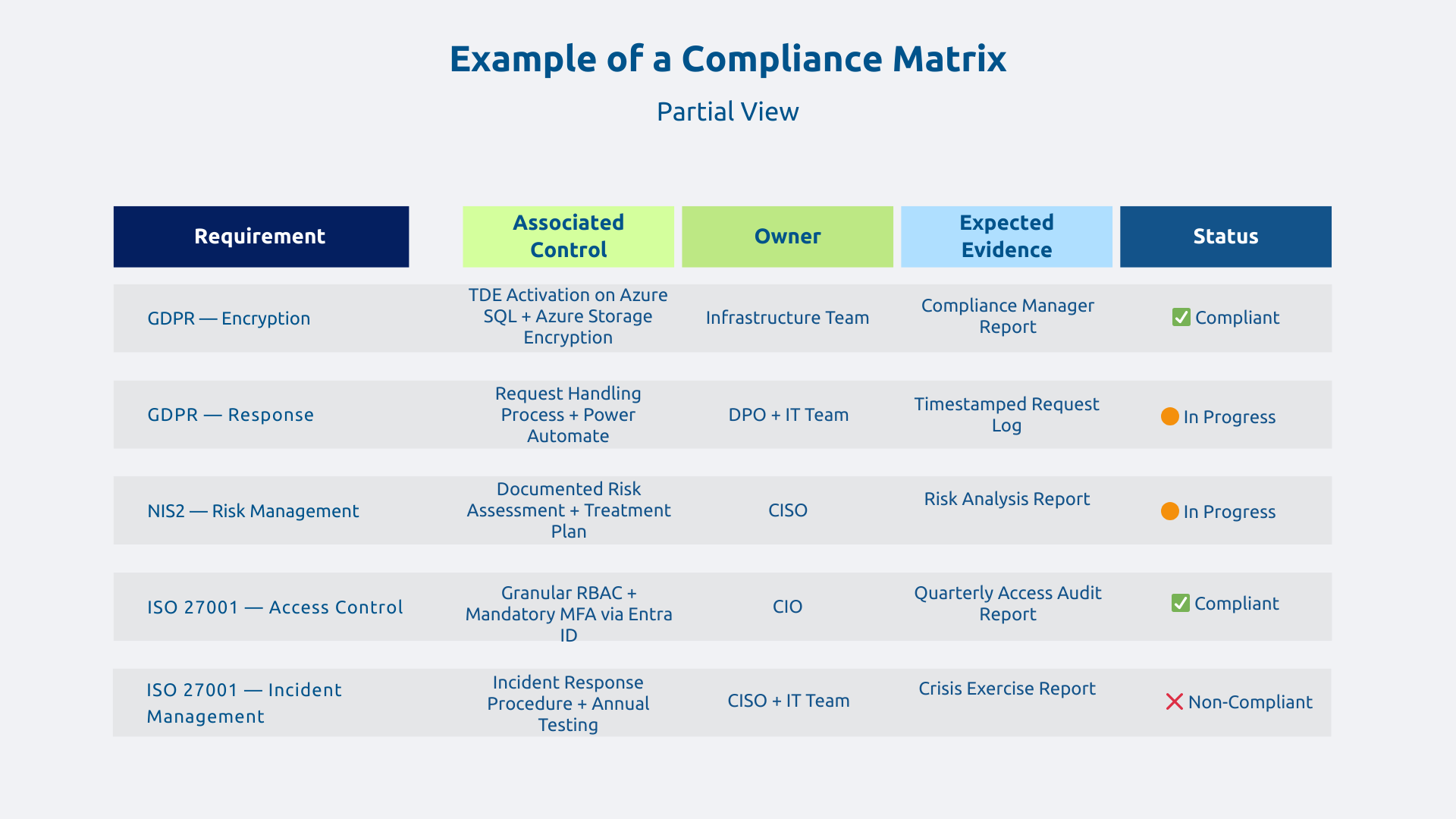
From this inventory, build a compliance matrix (requirement, associated control, responsible, expected proof, status) which becomes the backbone of your approach. This matrix makes it possible to rationally prioritize: legal requirements at criminal risk first, blocking standards for priority markets second, strategic certifications within 12-24 months in the third place.
Step 2 — Evaluate the gaps (gap analysis) and define an action plan
An internal or external compliance audit (the objectivity of an external perspective is often valuable) measures the differences between your current situation and the requirements identified. It often reveals more discrepancies than anticipated, in particular on traceability, documentation and formalized processes.
Each discrepancy is evaluated according to its criticality and the complexity of the remediation. The resulting action plan distinguishes between:
- The Quick Wins can be mobilized in less than 3 months (activation of existing functionalities, formalization of informal processes);
- structural projects over 3 to 9 months (deployment of new controls, implementation of governance);
- continuous improvement beyond that.
Management sponsorship is essential at this stage: compliance is a global governance issue and not just an internal IT matter.
Step 3 — Implement technical and organizational controls
On the one hand, the technical checks are automatable: encryption of data at rest and in transit, access management and strong authentication, event logging, verified backups.
On the other side, the organizational controls cover processes, training, documentation, and internal audits.
Let's take a concrete example: the GDPR requirement to encrypt personal data technically results in the activation of Azure Storage encryption, Transparent Data Encryption (TDE) on Azure SQL, and the deployment of Azure Information Protection for documents. The monitoring of these controls is then carried out via Compliance Manager.
Each check must be documented (who, what, how, when, proof) to be enforceable during an audit.
The Microsoft ecosystem to automate and simplify compliance
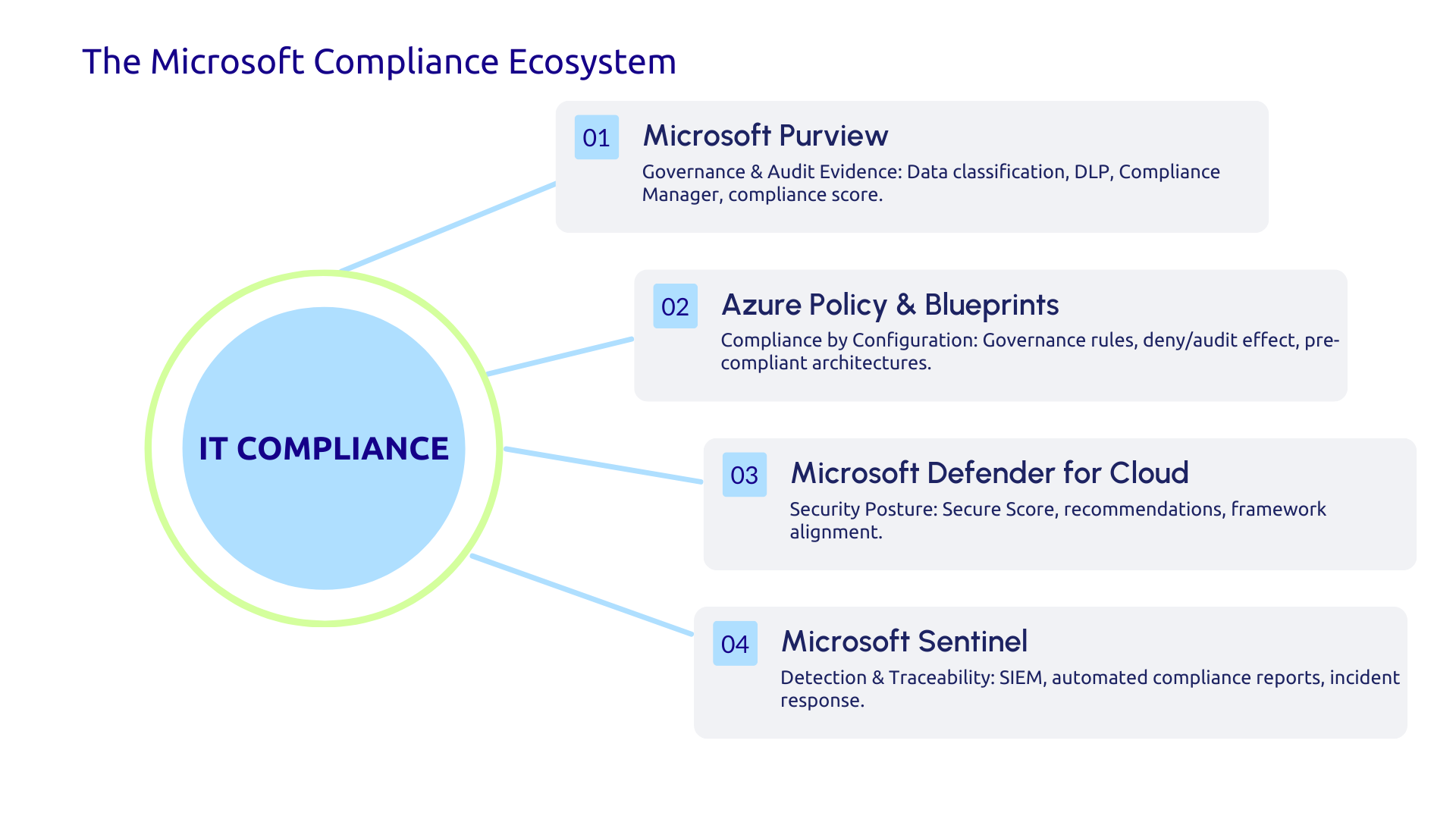
Microsoft Purview: the unified governance and compliance platform
Microsoft Purview centralizes governance and compliance across the entire Microsoft 365 ecosystem, Azure, and even third-party sources. Its features include automatic data discovery and classification, data loss prevention (DLP), information lifecycle management, eDiscovery, and auditing.
Sound module Compliance Manager, available in particular in the Microsoft 365 E3 and E5 offerings, is particularly interesting: it continuously assesses your level of compliance with predefined regulatory frameworks and generates a compliance score with prioritized actionable recommendations. Audit evidence is also centralized and accessible at any time, transforming preparation for audits lasting several weeks into a continuous and documented process.
Purview thus transforms compliance from a manual and periodic exercise into a largely automated and permanent process.
Azure Policy and Azure Blueprints: compliance through configuration
Azure Policy allows you to define and apply governance policies directly on Azure resources. You can require that all databases be encrypted, that resources be deployed only in European regions (data sovereignty requirement under the GDPR), or that no VM is exposed without a network security group. The effect Deny blocks non-compliant deployments before they even happen; the effect auditing alert on existing discrepancies.
Azure Blueprints allows you to deploy pre-configured architectures that comply with certified standards such as ISO 27001 or PCI-DSS, with all the policies and required configurations already integrated. Non-compliance therefore becomes structurally difficult since it is thought out from the very beginning.
Microsoft Defender and Sentinel: Continued Security Compliance
Of course, security compliance is not a one-time state. On the contrary, it is a continuous monitoring process. Microsoft Defender for Cloud continuously assesses the security posture of your Azure resources and provides a Secure Score aligned with the main compliance standards. Its actionable recommendations make it possible to improve the score in a gradual and measurable way.
Microsoft Sentinel, Microsoft's cloud-native SIEM, ensures the detection of security incidents and the traceability of events required by NIS2, PCI-DSS and other standards. The automated compliance reports it generates greatly simplify the burden of proof during audits. To deepen the detection and response dimension, the Microsoft Defender vs Sentinel article details the SIEM/XDR architecture.
IT compliance is no longer an option. Between RGPD, NIS2, ISO 27001 and industry standards, the complexity is real but manageable with the right approach. Purview automates assessment and audit evidence, Azure Policy ensures compliance by configuration, Defender and Sentinel provide continuous monitoring. These tools are not enough without clear governance: defined roles, management sponsorship, and fluid collaboration between IT, legal and business lines.
Do you want to assess your level of compliance and identify your priority risks? Contact Askware for a compliance diagnosis and turn your regulatory obligations into a competitive advantage.