SOC 2 certification: understanding the fundamentals
What is SOC 2 certification?
SOC 2 signifies Service Organization Control 2. This repository was developed by theAmerican Institute of Certified Public Accountants (AICPA), the professional association of American certified accountants, which defines several audit and certification standards in particular. Its objective is to assess the controls put in place by a service organization to protect its customers' data.
It is useful to specify that SOC 2 is not a certification in the strict sense of the word, unlike ISO 27001. It is a audit report produced by an independent external auditor, who reviews an organization's security controls and attests to their existence and effectiveness. Depending on the scope audited, a SOC 2 Type II report can reach several hundred pages detailing the controls tested, the results and the observations of the auditor.
The 5 Trust Services Criteria: the pillars of SOC 2
SOC 2 is based on five trust criteria, the Trust Services Criteria (TSC) :
- Security : protection against unauthorized access to systems and data. This is the only mandatory criterion in any SOC 2 audit.
- Availability (Availability) : accessibility of the system according to the commitments made (SLA).
- Processing Integrity : treatments are complete, valid, accurate, timely, and authorized.
- Confidentiality (Confidentiality) : protection of information designated as confidential.
- Privacy (Protection of privacy) : collection, use, storage, disclosure and deletion of personal data in accordance with the organization's commitments.
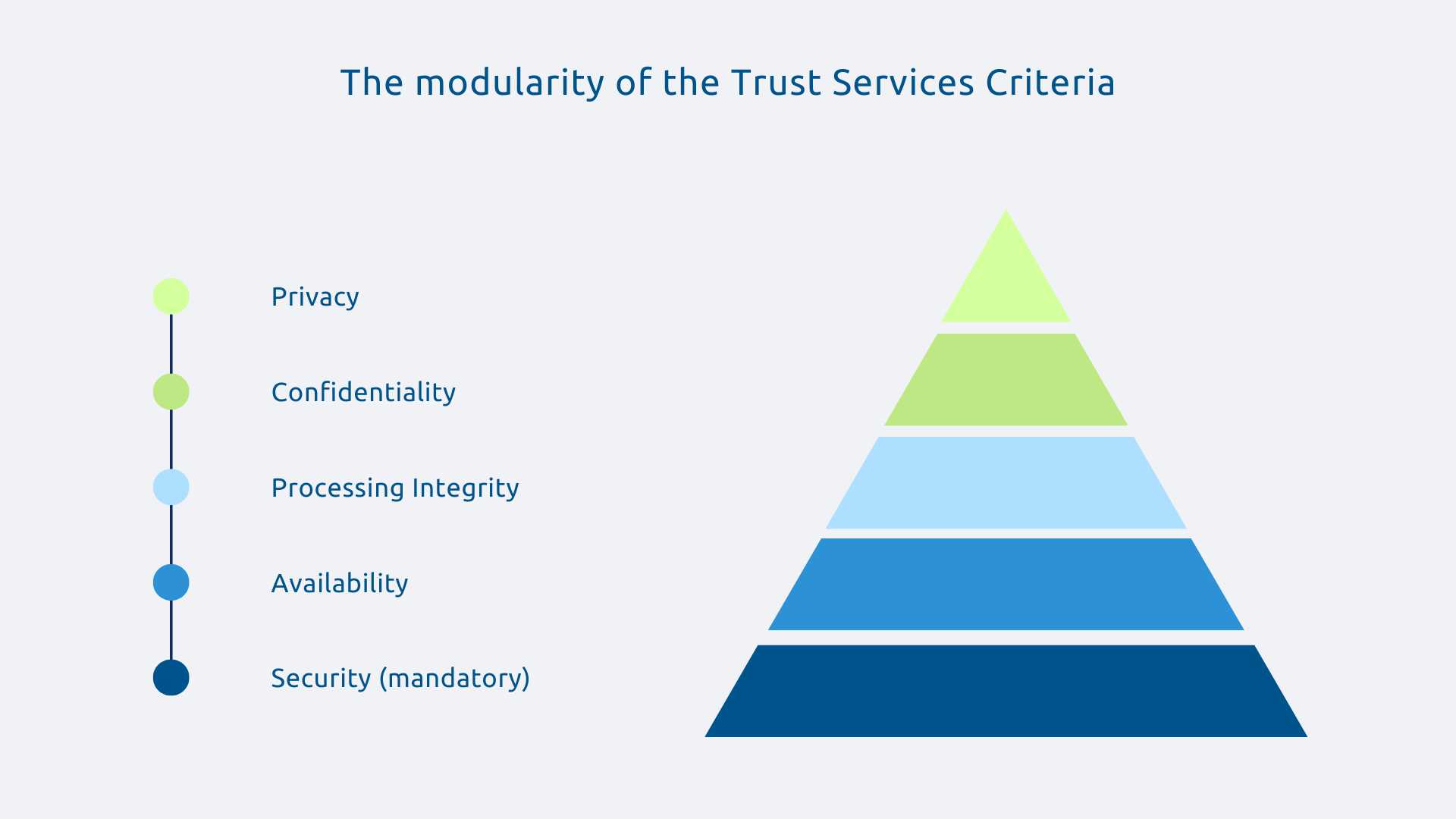
This modularity makes SOC 2 particularly suitable for cloud providers, whose commitments vary according to the services offered.
SOC 2 Type I vs SOC 2 Type II: what is the difference?
The distinction, while fundamental, is often misunderstood.
The SOC 2 Type I Evaluate the design controls at an instant T. It answers the question: “Are these controls well designed?” This is useful for an initial assessment or at the beginning of a business relationship.
The SOC 2 Type II goes much further: it assesses the operational effectiveness of controls over an observation period of at least six months, most often around twelve months. It answers the question: “Do these controls really work over time?” It is this report that is expected for serious and long-term commitments.
Microsoft Azure has a SOC 2 Type II report that is renewed regularly, attesting that security controls are not only designed, but also tested over an extended audit period. To seriously evaluate a cloud provider, always require Type II.
SOC 2 vs ISO 27001: differences and complementarities
Origin and geographical scope
ISO 27001 is a international standard developed by the International Organization for Standardization (ISO). SOC 2 is a American standard developed by the AICPA, which is now particularly valued in cloud IT architecture and in commercial relationships with North American companies.
In practice, ISO 27001 is one of the reference standards in Europe for information security management, frequently mentioned as a criterion in public tenders or compliance procedures. SOC 2 dominates in the United States and is highly valued by tech companies and SaaS publishers.
That said, when a French company wants working with an American SaaS publisher, it may require a SOC 2 report to ensure that security controls are not only in place but also effective over time.
To summarize, if you are targeting the American market or Anglo-Saxon partners, SOC 2 becomes almost indispensable. If you operate mainly in Europe, ISO 27001 will be required more often. Global players like Microsoft own both, and that's no coincidence.
Audit approach and methodology
ISO 27001 certifies a Information Security Management System (ISMS). The organization defines its own perimeter, security goals, and risks. The audit verifies that this system is properly implemented and continuously improved (PDCA cycle). The deliverable is a public certificate.
SOC 2, on the other hand, assesses the operational and technical controls of a service provider in relation to the Trust Services Criteria defined by the AICPA. The deliverable is a detailed audit report that describes each control tested and its effectiveness over the observation period.
ISO 27001 certifies that a safety management system is in place and audited, while SOC 2 provides a detailed report describing the controls and their effectiveness over a given period of time. Both approaches are rigorous but they shed light on different perspectives.

Complementarity in the Microsoft ecosystem
Microsoft has numerous international certifications including:
- ISO 27001;
- ISO 27017;
- ISO 27018;
- SOC 2 Type II;
- PCI-DSS;
- HDS for certain Azure infrastructures in France.
Concerning ISO 27001, the standard provides the strategic and organizational vision: Microsoft has a structured, managed and continuously improved security management system. SOC 2, for its part, goes down to the operational level: for each Azure, Dynamics 365 or Power Platform service, an independent auditor has verified that the technical controls really work over time.
For a DSI which must justify the choice of Azure to its auditors, ISO 27001 provides the overview while the SOC 2 report makes it possible to detail the specific controls put in place on the services actually used. The two certifications reinforce each other.
SOC 2 in the Microsoft ecosystem: what this guarantees in practice
Microsoft services covered by SOC 2
Microsoft's SOC 2 reports cover major services such as Azure, Microsoft 365, Dynamics 365, and Power Platform, according to the scope defined in each audit report. Each service is subject to a specific evaluation.
These reports are accessible via the Service Trust Portal, after authentication with a professional Microsoft account and acceptance of the access conditions, some resources requiring a confidentiality agreement. If you're deploying Dynamics 365 Sales for your sales force, the report will detail access, encryption, monitoring, and incident response controls specific to this service.
Trust Services Criteria applied to your Dynamics 365 and Power Platform projects
The value of SOC 2 lies in its granularity by service. For a Dynamics 365/Power Platform project, here is what each criterion guarantees in concrete terms:
- Security : Dataverse access controls (RBAC), MFA authentication via Microsoft Entra ID, anomaly detection and incident response.
- Availability : Microsoft announces for most Dynamics 365 services an availability SLA of 99.9%, according to the conditions defined in Microsoft service level agreements, with geographic redundancy and 24/7 monitoring.
- Processing Integrity : validation of Power Automate workflows, traceability of changes, integrity of data flows between services.
- Confidentiality : data encryption at rest and in transit, Data Loss Prevention (DLP) Power Platform, tenant isolation.
- Privacy : GDPR compliance, personal data management tools, Data Processing Contractual Addendum.
SOC 2 is not content with theoretical guarantees: it verifies that these controls really work, on the services that your teams use on a daily basis.
The shared responsibility model revisited from a SOC 2 perspective
Microsoft SOC 2 covers infrastructure and platform part : the physical security of data centers, the availability of the underlying infrastructure, the operational controls of cloud services. It is a solid but insufficient base.
Even with SOC 2, you remain fully responsible for:
- configuring security controls (MFA, Conditional Access, DLP);
- the governance of access and roles in your environments;
- the classification and protection of your business data;
- training and raising the awareness of your users;
- auditing and monitoring from your own tenant.
Microsoft guarantees via SOC 2 that the Dataverse infrastructure is secure. But if you set up permissions that are too broad in your Dynamics 365 environment, Microsoft SOC 2 won't protect you from this misconfiguration. Supplier certification is an essential foundation, not a blank check.
Why SOC 2 is important for your organization
Contractual requirements and tenders
SOC 2 is required more and more frequently in B2B with American companies or international groups, in regulated sectors (finance, health, tech) as well as in tenders from organizations that are mature in terms of security.
More and more European companies, under the influence of their American parent companies or their international customers, are integrating SOC 2 into their criteria for qualifying cloud providers. Not working with a SOC 2 certified supplier can you disqualify certain business opportunities, even if your own organization is ISO 27001 certified.
Due diligence and supplier risk management
Assessing the security of a cloud provider in depth is time consuming, expensive, and technically complex. Fortunately, SOC 2 radically simplifies this process.
Instead of sending a 200-question questionnaire to Microsoft and waiting for self-reporting responses, you can request the SOC 2 Type II report : a document produced by an independent external auditor, updated regularly, which details precisely the controls tested and the results obtained. SOC 2 pools evaluation efforts and provides independent assurance that no internal response can replace.
Competitive advantage and market differentiation
For IT integrators and service providers, relying on SOC 2 certified suppliers is becoming a commercial argument in its own right. Askware can rely on Microsoft infrastructures with recognized certifications (such as ISO 27001 or SOC 2 Type II) to ensure that the technical platforms used in its projects are based on audited environments.
In sectors where safety is a selection criterion, it is a concrete differentiator.
SOC 2 and ISO 27001 form a complementary duo: one validates the security management system as a whole, the other attests to the operational effectiveness of the controls service by service. Microsoft has both, offering a two-tier level of assurance that few cloud providers can offer. Exploiting these guarantees intelligently in your Microsoft projects requires understanding their scope, limits, and coordination with your own governance.
Beyond SOC 2 and ISO 27001, the Microsoft certification ecosystem is still expanding: ISO 27017 for cloud security, ISO 27018 for the protection of personal data in the cloud, HDS for health, PCI-DSS for payments... These are all standards that, depending on your sector and your customers, can become decisive criteria.
Need help interpreting Microsoft security certifications or structuring your compliance strategy? Contact the Askware experts for an exchange.